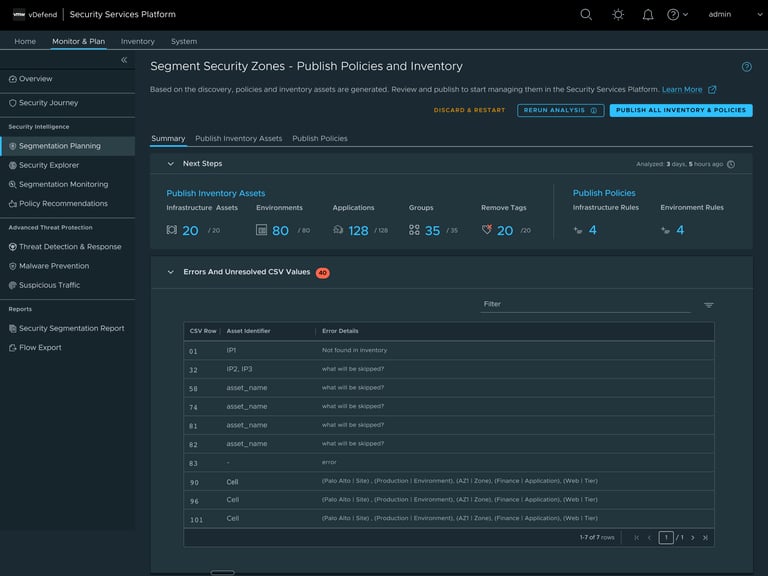
Segmentation Planning
Redesigning a high-complexity onboarding workflow mid-development to establish a scalable platform foundation.
Role
Senior Product Designer
Timeline
Feb 2025 - Nov 2025
Platform
VMware Security Services Platform
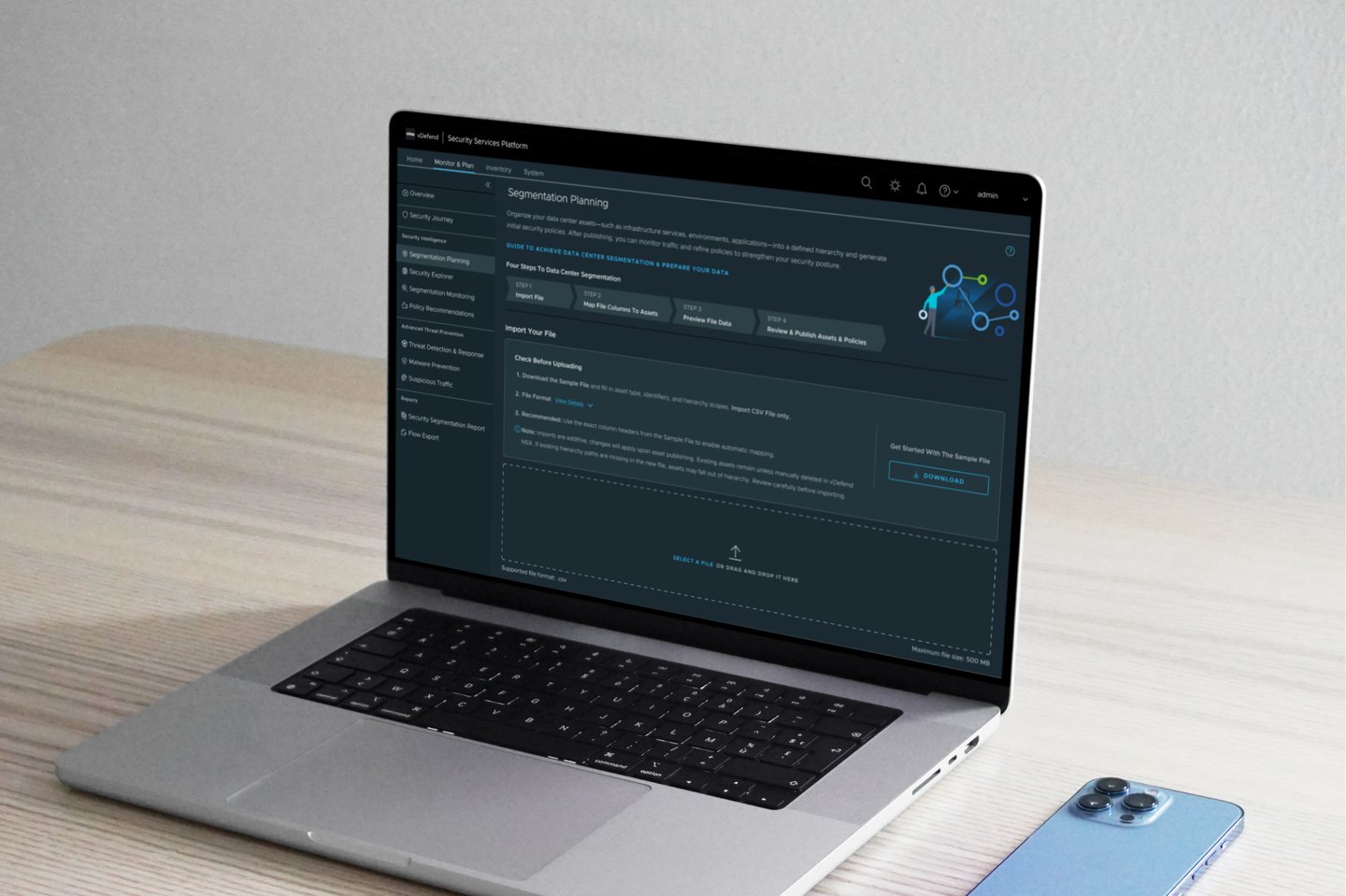

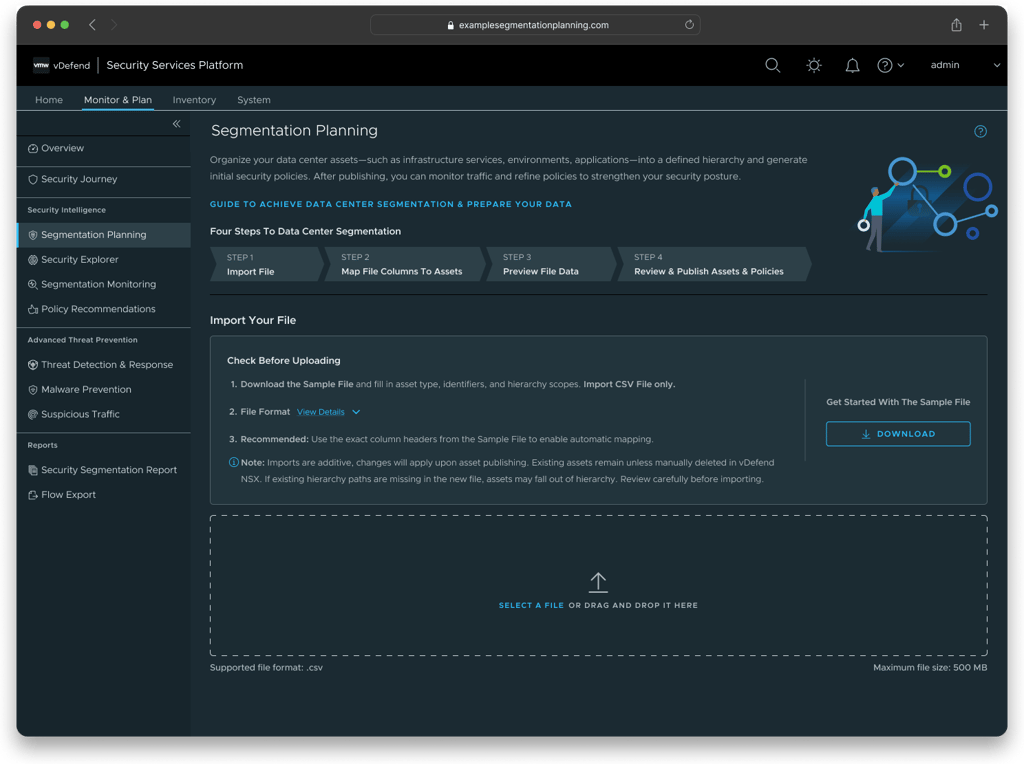
Segmentation Planning is a core onboarding workflow for the VMware Security Services Platform. It enables security administrators to import data, define hierarchy, publish inventory assets, and establish security policies at scale.
When I joined the project, the feature was midway through development. The workflow was largely implemented, but internal reviews and testing identified recurring issues: critical steps were error-prone, and the system lacked sufficient visual feedback to help users understand progress.
Introduction
A Critical Foundation for Secure Infrastructure
Recurring bugs exposed deeper architectural misalignment.
When I joined the project, the feature was midway through development. The workflow had already been implemented, but internal reviews and testing surfaced recurring issues:
CSV import and mapping were error-prone
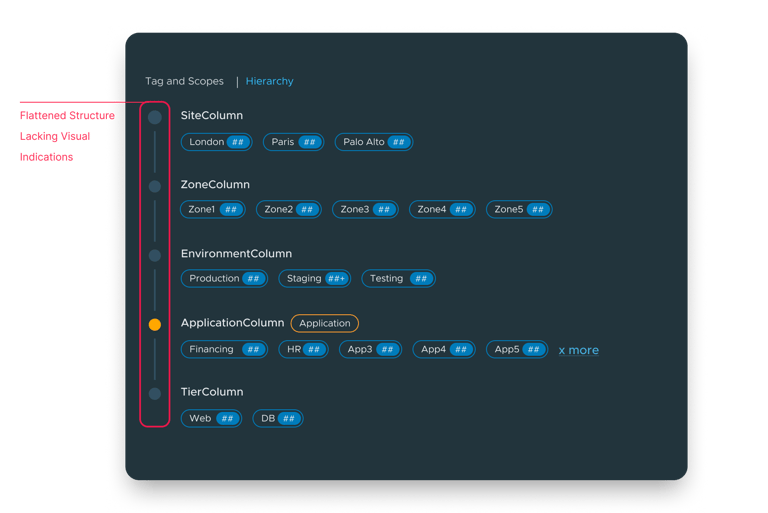
Hierarchy definition lacked clear visualization
Large datasets triggered long backend analysis with minimal system feedback
Where The Workflow Began To Strain
Landing Screen
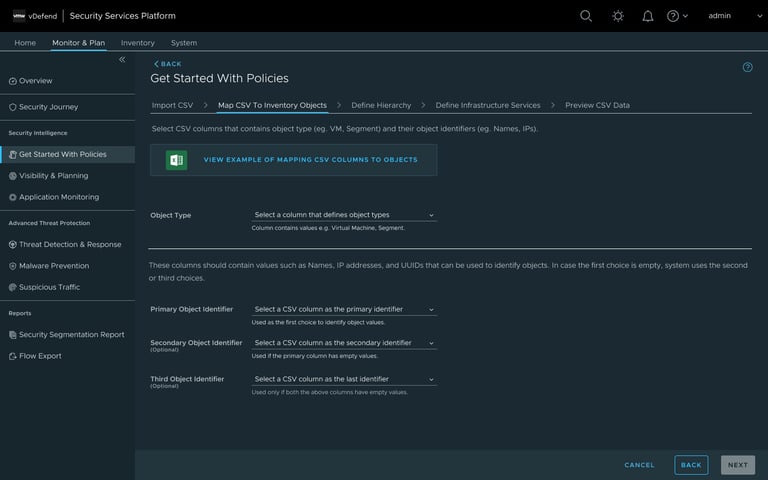
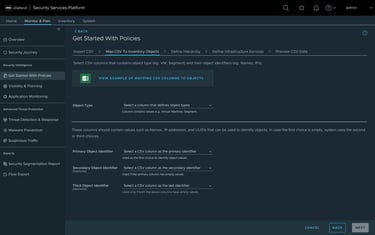
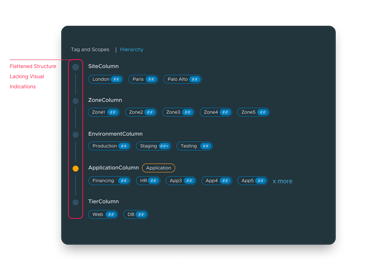
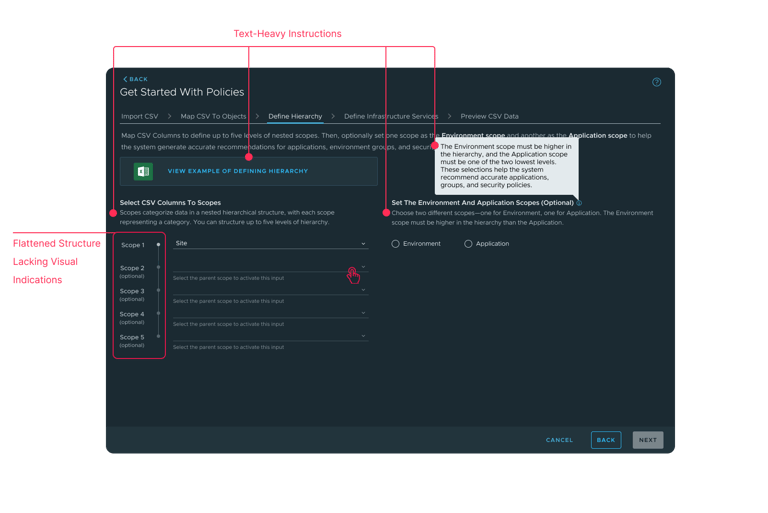
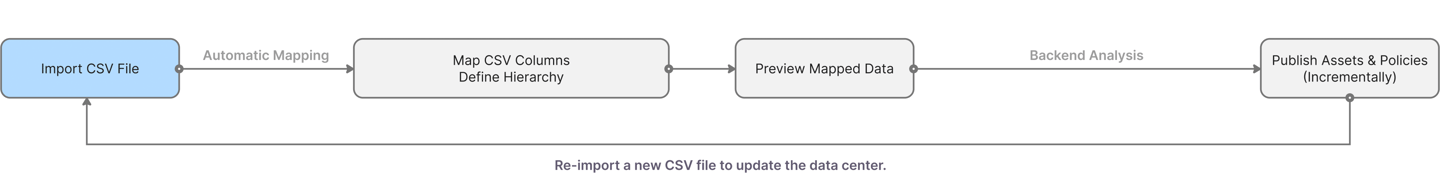
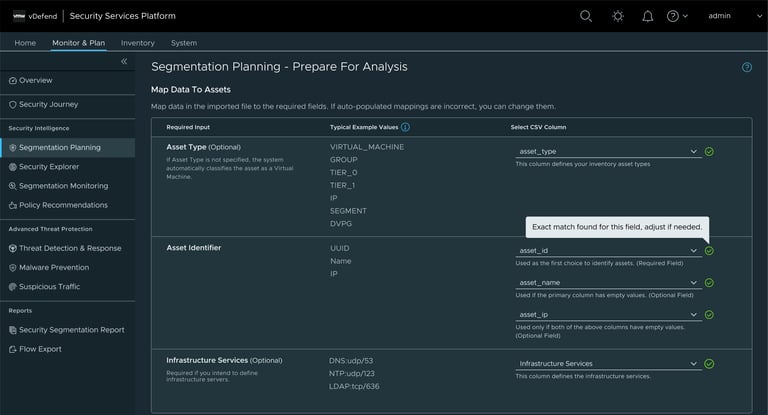
Step 2: Map CSV Columns To Assets
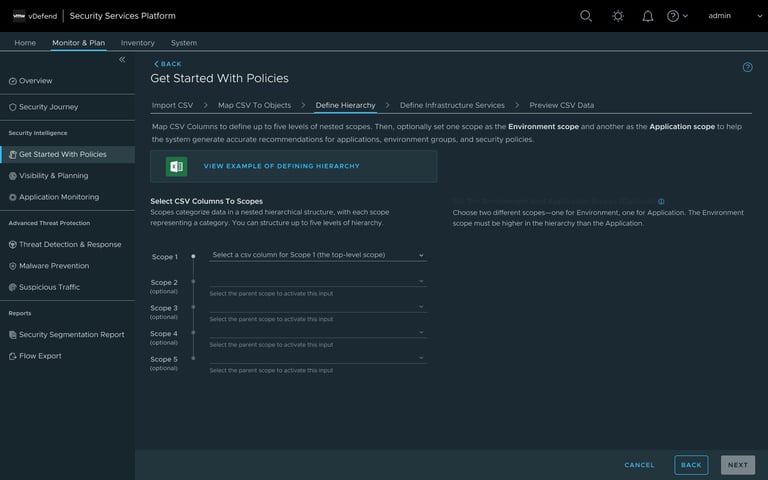
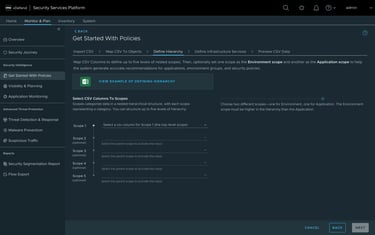
Step 3: Define Hierarchy
Individually, these appeared solvable. Together, they revealed a structural issue: the workflow required users to understand complex system internals without a coherent set of instructions and a clear mental model.
Initial UX efforts focused on localized improvements — tooltips, labels, micro-adjustments. However, each fix added surface clarity while increasing cognitive load. I began by redesigning the most critical step — CSV column mapping — aligning layout directly with backend logic.
Through cross-functional reviews with PMs, QE, backend, and frontend engineers, I advocated for a structural shift rather than continued patchwork.
We aligned on a Proof of Concept, secured leadership approval for the revised direction, and extended the project timeline to support a foundational redesign.
This marked the turning point.
Addressing symptoms increased complexity...To resolve the structure, the user flow needed to be rethought.
From Incremental Fixes to Architectural Reset
Redefining The Challenge
How might we enable users to confidently transform complex CSV data into a reliable security inventory—without requiring them to understand the underlying system complexity?
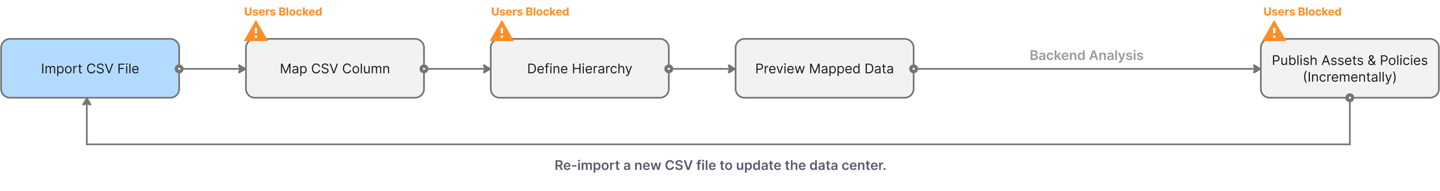
The original workflow consisted of five disconnected steps handling related configuration details. This fragmentation made progress difficult to understand and recovery from errors.
Steps were realigned with the system's logic to support contextual decision-making
Before
After
A Clearer Workflow Architecture
The redesign consolidated related decisions into a coherent three-stage structure:
Import file → Map CSV columns → Preview imported data
By aligning step boundaries with how the backend processes data, users could act with context rather than speculate about downstream effects.
Layout Designed Around System Relationships
Instead of grouping input fields across many steps, the interface layout was reorganized using a top-down layout that provides an example value and the input field.
This reduced cross-referencing between steps and made structural dependencies visible within a single decision space.
Hierarchy definition and column mapping inputs were organized to reflect how the system interprets the data.
Before
After
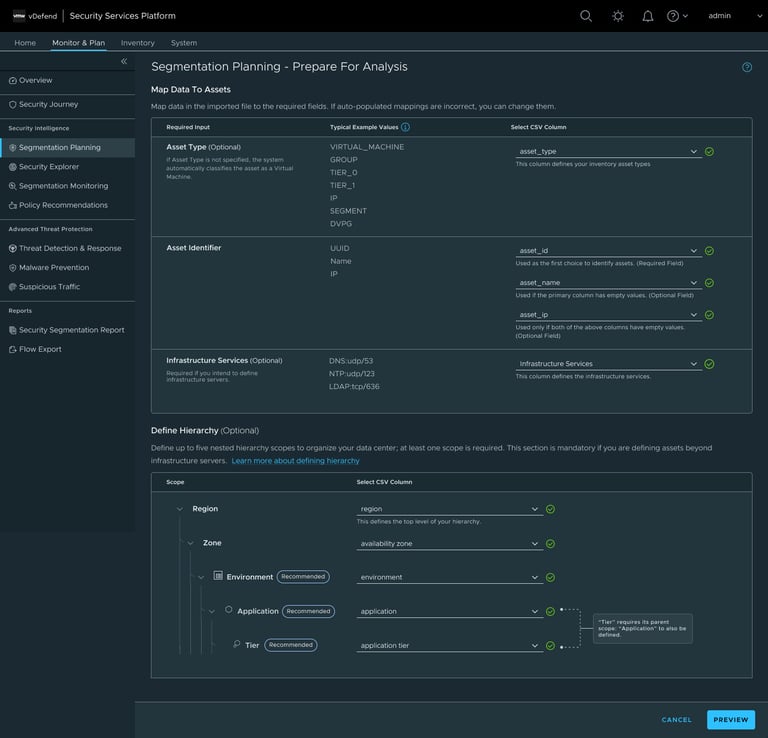
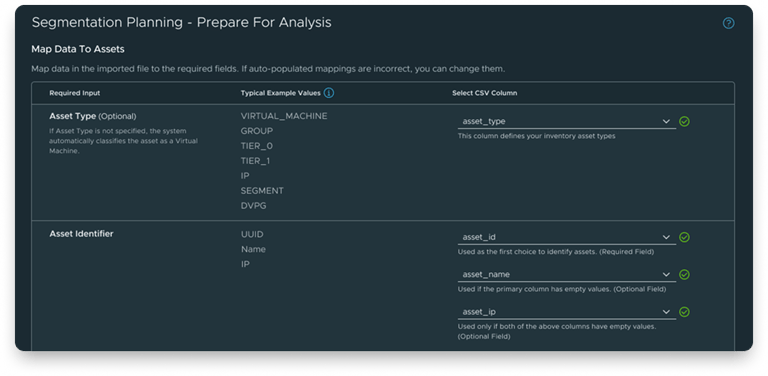
Layout reorganized to provide structural information for each input field.
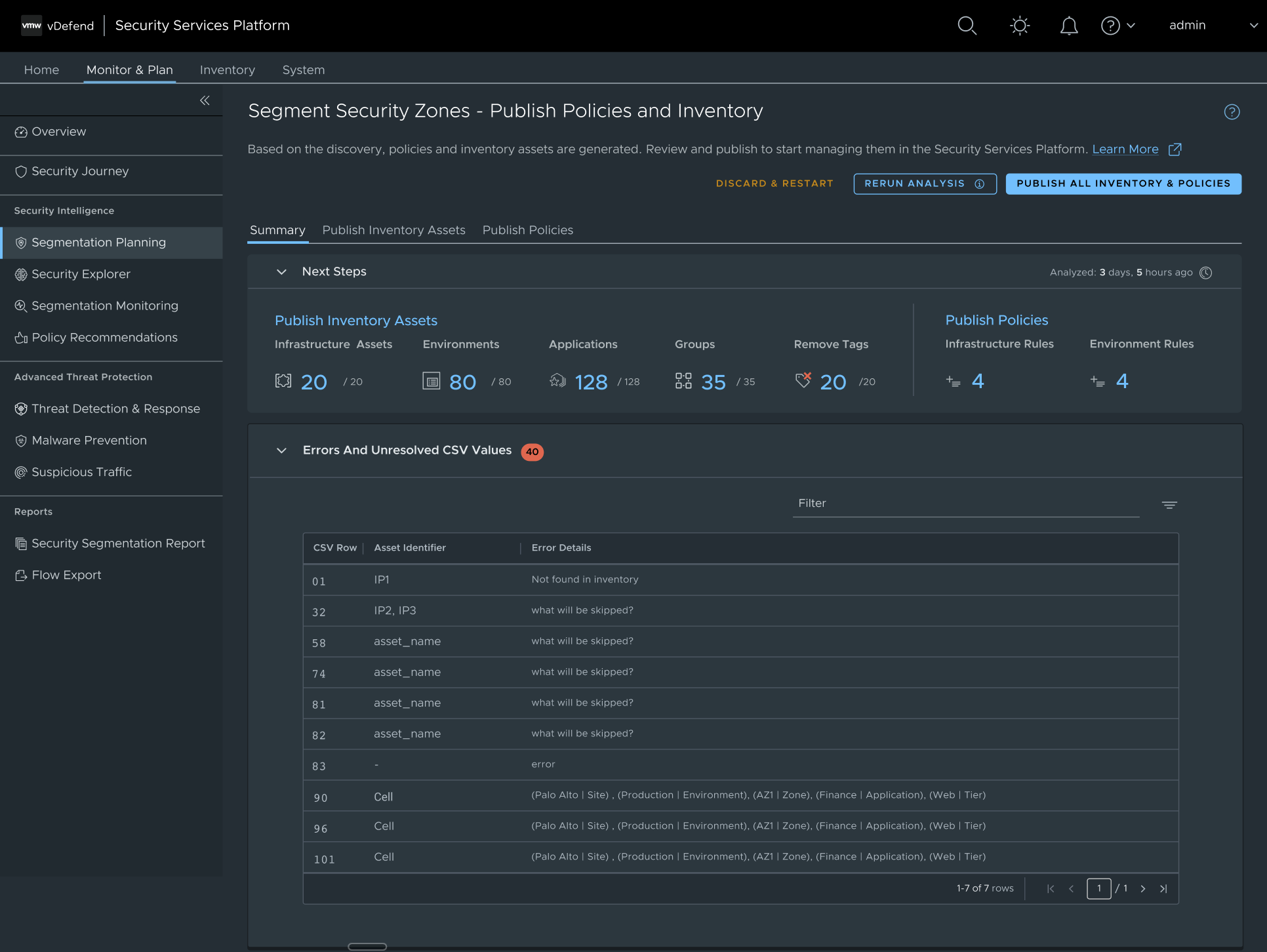
System Feedback at the Right Moments
Previously, backend validation occurred late in the workflow. For large datasets, analysis could take more than 30 minutes, leaving users unsure whether progress was being blocked.
The redesign introduced:
Immediate CSV validation states
Column-level error surfacing during mapping
Explicit backend processing indicators
Users could now correct issues before committing to irreversible configuration steps.
Validation and processing states were surfaced early to prevent costly rework.
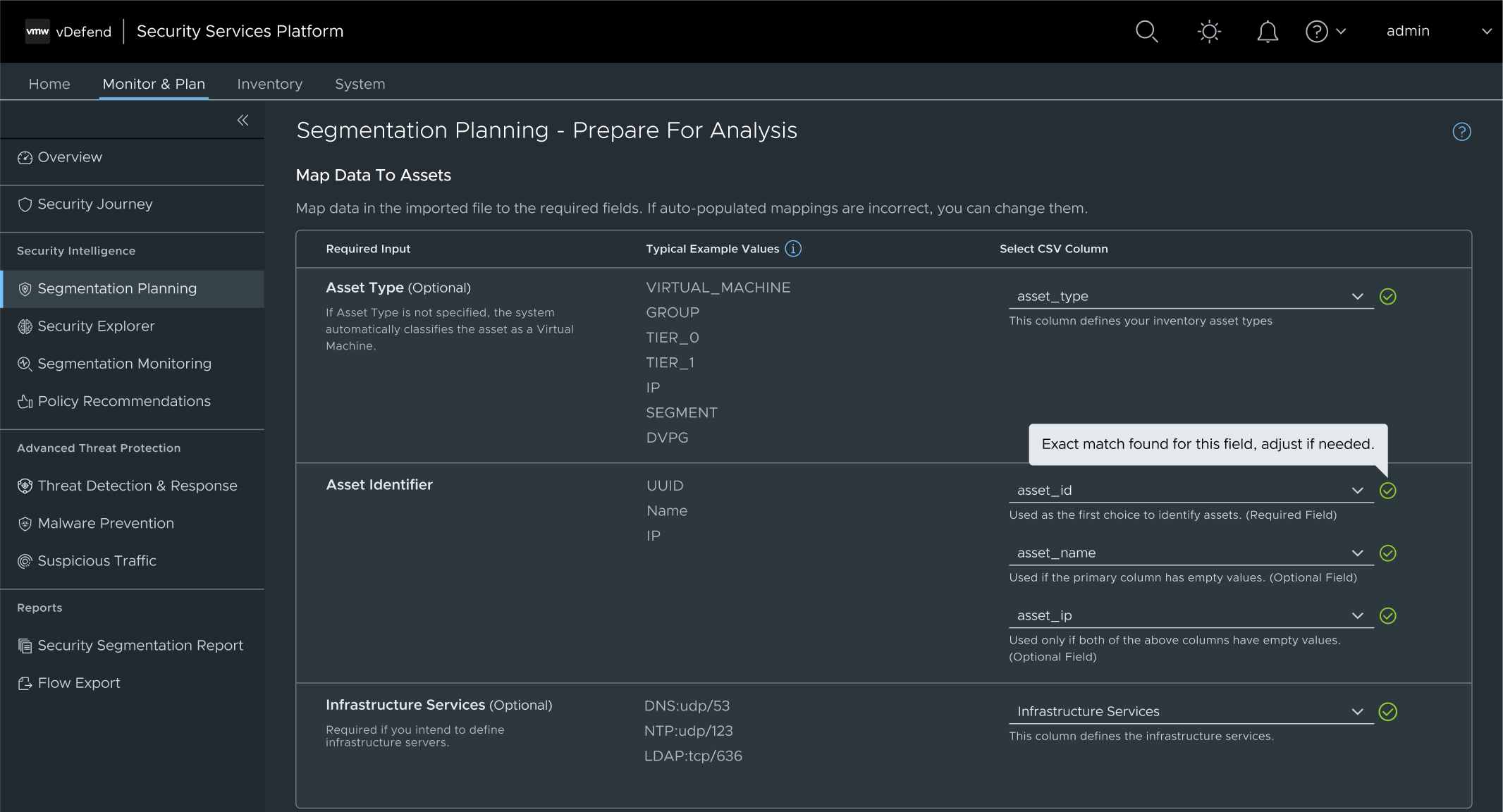
Automation Without Loss of Control
Rather than abstracting away complexity, automation was applied selectively:
Automatic progression after successful validation
Auto-mapping with editable confirmation
Traffic-detected VM recommendations surfaced contextually in Preview
The system reduced repetitive effort while ensuring administrators retained control over security-sensitive decisions.
Predictable system behavior was automated while preserving user oversight.
Supporting Adoption Beyond The UI
Given the workflow’s complexity, I authored a concise two-page guide explaining:
End-to-end system logic
CSV requirements
Hierarchical modeling principles
Partnering early with the documentation team ensured alignment. The guide is now frequently used by Sales during customer onboarding to clarify system behavior.


Shared mental models help teams explain complex infrastructure logic to customers.
The Results
Shipped November 2025 as a foundational capability Security Services Platform 5.1
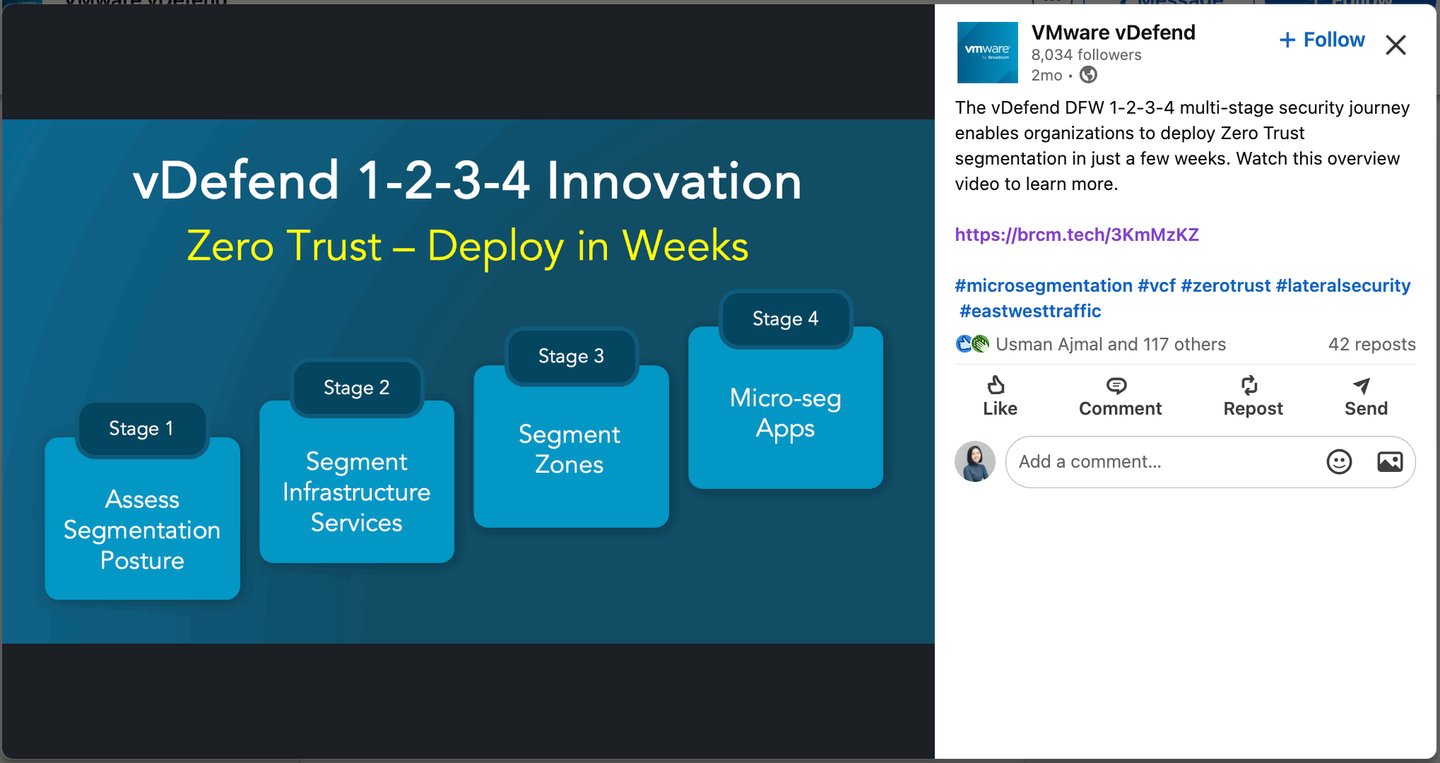
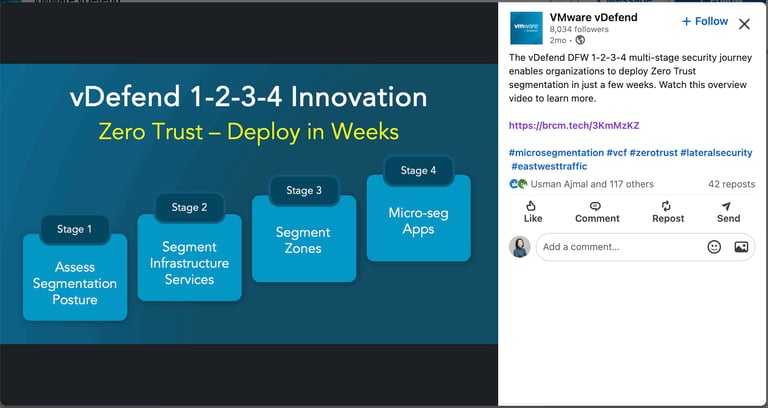
The redesigned workflow now underpins:
Data center asset creation
Recommendations for distributed firewall configuration
Traffic-detected VM recommendations
Leadership described it as one of the most consequential releases for the platform, establishing a stable base for future segmentation features.
Personal Impact & Learnings
Leading structural change required balancing the architectural concept, cross-functional team alignment, and delivery risk.
This project expanded my role beyond interface design.
Advocating for a structural reset meant:
Challenging incremental solutions mid-development
Aligning backend engineering constraints with UX direction
Securing leadership buy-in for timeline extension
Translating complex infrastructure logic into a coherent mental model
The experience reinforced the importance of diagnosing systemic friction early — and the responsibility of design to reshape architecture when surface clarity is insufficient.

